Cyberattack waves wash over West African banks
It’s crime time again as banks and other financial institutions in several West African countries have been targeted by cyber criminals.
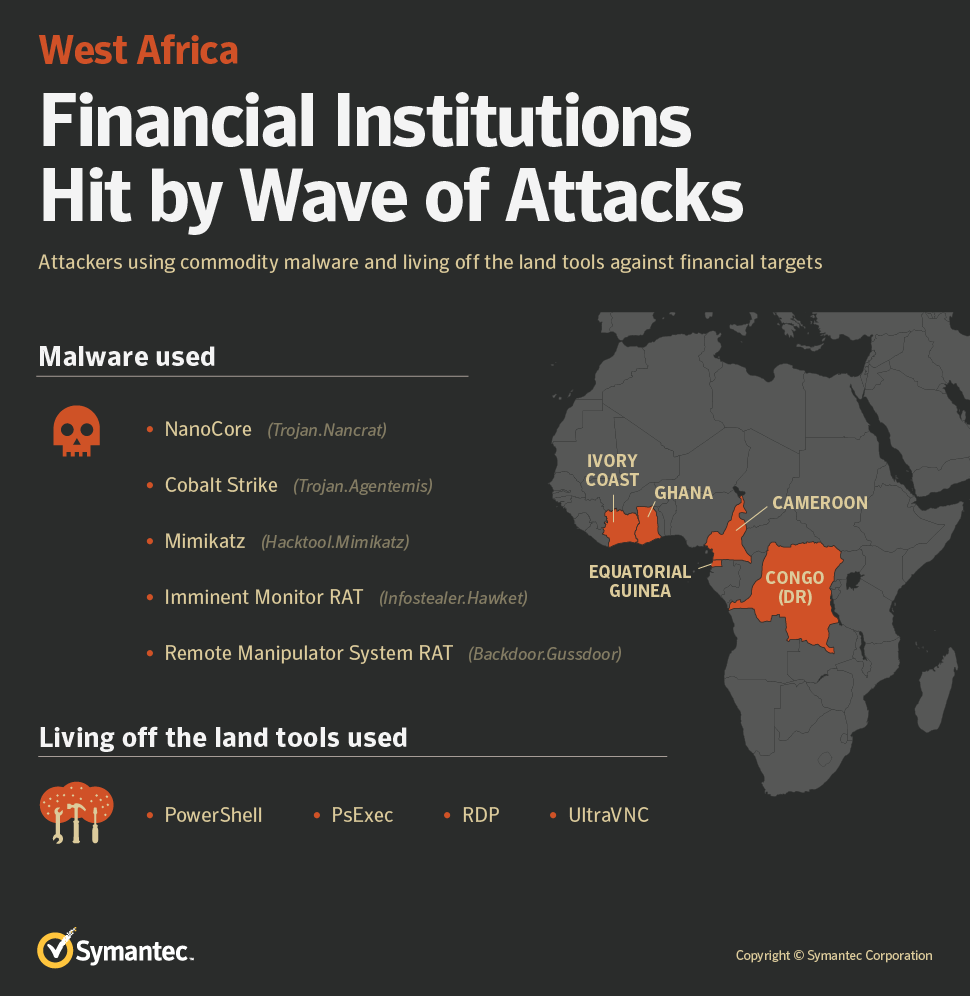
According to Symantec, the attacks have been underway since at least mid-2017. To date, organisations in Cameroon, Congo (DR), Ghana, Equatorial Guinea, and Ivory Coast have been affected. (An infographic is below.)
The attackers used a range of commodity malware and living off the land (LotL) tools. The latter refers to the use of operating system features or network administration tools to compromise victims’ networks.
Who is behind these attacks remains unknown. Symantec says they could be the work of a single group or, more likely, several different groups employing similar tactics.
The firm has observed four distinct attack campaigns.
The first has been underway since at least mid-2017 and has targeted organisations in Ivory Coast and Equatorial Guinea. The attackers infected victims with commodity malware known as NanoCore (Trojan.Nancrat) and were also observed using PsExec, a Microsoft Sysinternals tool used for executing processes on other systems, on infected computers.
Lure documents used by the attackers referred to a West African bank which has operations in several countries in the region. Some tools used in these attacks are similar to tools mentioned in a 2017 Swift alert, indicating the attackers may have been attempting to perform financial fraud.
The second type began in late 2017 and targeted organisations in Ivory Coast, Ghana, Congo (DR), and Cameroon. The attackers used malicious PowerShell scripts to infect their targets and also used the credential-stealing tool Mimikatz (Hacktool.Mimikatz). They also made use of UltraVNC, an open-source remote administration tool for Microsoft Windows.
The attackers then infected computers with the commodity malware known as Cobalt Strike (Trojan.Agentemis) which is capable of opening a backdoor on the computer, communicating with a command and control (C&C) server, and downloading additional payloads.
The third was directed against an organisation in Ivory Coast. It had also been targeted by the second campaign. In this case the Remote Manipulator System RAT (Backdoor.Gussdoor), alongside Mimikatz and two custom Remote Desktop Protocol (RDP) tools. Since Mimikatz can be used to harvest credentials and RDP allows for remote connections to computers, it’s likely the attackers wanted additional remote access capability and were interested in moving laterally across the victim’s network.
The fourth began in December 2018 and was directed against organisations in Ivory Coast. The attackers used off-the-shelf malware known as Imminent Monitor RAT (Infostealer.Hawket).
As you’d expect – and because Symantec is talking about it – all four attack types were first discovered through alerts generated by its Targeted Attack Analytics (TAA).
TAA use artificial intelligence (AI) to analyse Symantec’s data lake of telemetry in order to spot patterns associated with targeted attacks.
Until now, Symantec has seen relatively little evidence of these kinds of attacks against the financial sector in West Africa. However, it now appears that there is at least one (and quite possibly more) groups actively targeting banks in the region.














































I expected something like this a long time ago. African institutions generally place little or no priority on cyber-security.